Why I am leaving LastPass for another password manager?
I have recommended LastPass for years as a password manager after their last few cyberattacks, their handling of the attacks, and the way they have handled password storage and security I cannot recommend them. I myself have decided to all my passwords to BitWarden.
How BitWarden Stores Passwords?
The way BitWarden handles the encryption of passwords is very good. To start with they have a secret key feature so even if someone would get your password database and your master password they still cannot decrypt it without the secret key. If they should get the secret key and your password database, they still cannot decrypt your passwords because they do not have your master password.
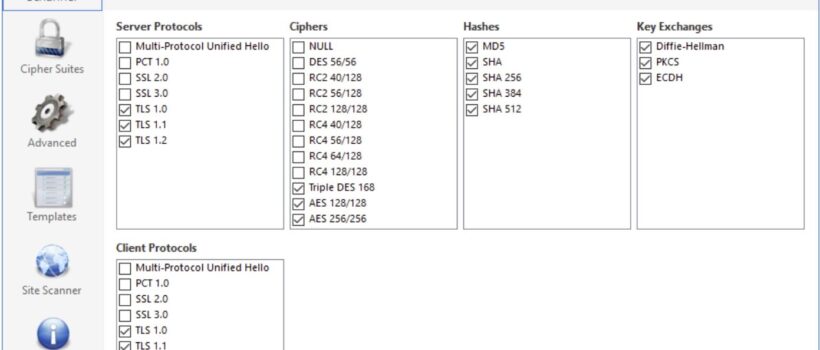
BitWarden uses sha-256 to derive the encryption keys from your master password. BitWarden salts and hashes your master password with your email address locally before transmission to our servers once a bit Warden server receives the hashed password it is salted again with a cryptographically secure random value hashed again and stored in their database. The default iteration count used with pbkdf2 is one hundred thousand and one iteration on the client client-side iteration count is configurable from your account settings and then an additional 100,000 iterations when stored on our servers for a total of 201,000 iterations by default.
These two methods make password storage very secure. BitWarden has publicly released its third-party security audit schedule and is registered with the HackerOne bug bounty program making their security constantly tested.
Is BitWarden Free or Paid?
BitWarden has personal and business plans. The business plans are starting at three dollars and go up from there. I personally only focused on personal plans which have three price points.
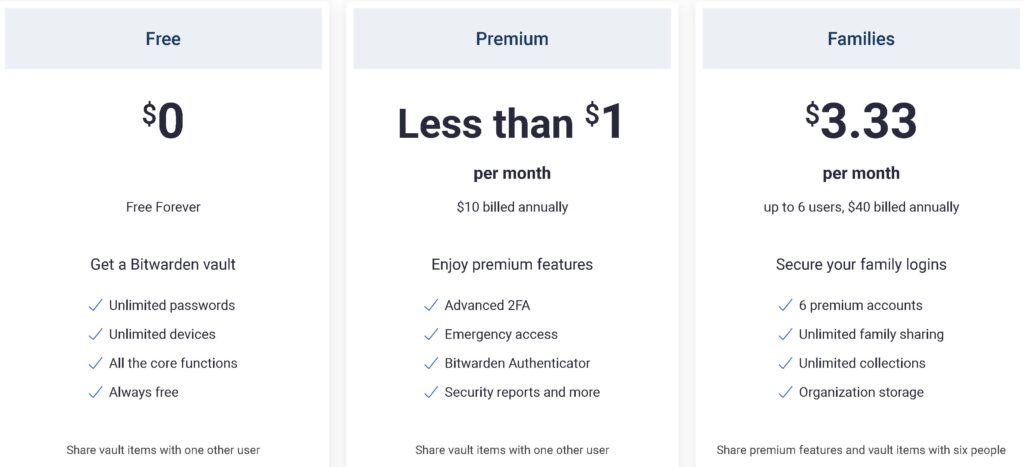
BitWarden is again open source so they offer a free plan with unlimited passwords, and unlimited devices and will be free forever. Most password managers do not offer a free plan, so this was very impressive.
Their next plan is the one I went with which offers all free features but includes two-factor authentication, BitWarden Authenticator, security reports, and emergency access for ten dollars a year. You will also get 1 gig of encrypted storage on BitWarden with this plan which can be important for personal documents and things like certs or codes if you are like me.
The third tier is a family plan for forty dollars a year, including family sharing, six accounts, and more storage.
Which plan to get?
I personally went with the ten-dollar-a-year plan. I don’t agree with BitWarden charging for 2FA authentication, but I feel this is worth the money plus this is a way of supporting the open-source community. I found out later how cool the BitWarden Authenticator is when you install their software on your Mac and PC. The authenticator is part of the ten-dollar-a-year plan and having a right-click authenticator tool is very handy. I was interested as well in the security reports.
Is migrating from Lastpass to BitWarden hard?
No, it’s very easy I recommend downloading the LastPass app for windows or mac. Then go to advanced options and click export. Make sure to export to a . CSV file. Once that is done go to BitWarden login and click on tools and import select the LastPass .csv option get the file you just exported from LastPass and hit import. Once you have verified all your passwords and notes are in BitWarden delete and empty your trash of the export you did from LastPass you do not want that file on your machine.
Now we need to protect ourselves from any further LastPass attacks go to
https://lastpass.com/delete_account.php
Here you can completely delete your account or reset your account to default either way you should do this once you are sure everything you need is in BitWarden.
How is using BitWarden?
Just like LastPass, BitWarden has extensions for all browsers and has local software you can install as well. When you install the software on your computer you get a right-click menu that allows you to authenticate using the BitWarden Authenticator which was very handy. I would rate BitWarden faster and less bloated than LastPass and the functionality is just as good as well.
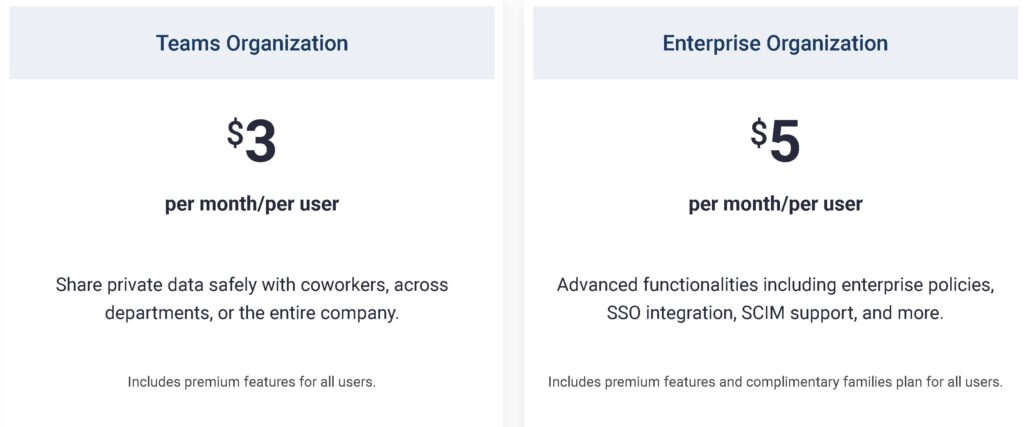
Can I use this for business?
One thing I did not know until I started doing research is that you can host your own BitWarden server if you wanted since it’s open source. While this would be fun to do the cost of renting a VPS or even running it on my home server does not seem worth the effort for 10 dollars a year.
I could see this being a solution for a big company with a lot of users as this would cut the cost down for them since they would not be paying three to five dollars a user per month. If I was a larger company I could see this being a good solution and I may recommend this to large corporate customers. For small business customers, I would recommend the business plan or even the family plan might work out with less hassle and ease of use.
Will it work on my smartphone?
BitWarden has an iPhone and Android client that you can you use to store and get passwords. The app does support FaceID unlocking, fingerprint unlocks, passcode unlocking, Apple Watch, and many other features you would expect for an app in the mobile world. The app does have a sync feature so if you save a password on your desktop it will sync to the phone or from the phone to the desktop. The app has a password generator and password autofill feature if you would rather use BitWarden than the built-in Apple or Android password generator. The BitWarden app has a neat feature called send where you can send an encrypted message link and then will delete it in so many days protected by a password. Which could be handy for sharing passwords or personal documents with users.
Final Thoughts
I think BitWarden is a much better replacement and a much more secure option than LastPass. The software has more options seems to be less buggy and is 1/3 the price a year of LastPass.